Blog
3 key security considerations for autonomous material handling solutions

The manufacturing industry has consistently been one of the most targeted sectors for cyberattacks, accounting for 23% of all ransomware attacks in 2021. With breaches averaging $5.56M USD—13% above the global average—and downtime lasting 21 days, manufacturers must ensure that every new technology is securely integrated to reduce exposure to risk in an industry facing persistent cyber threats.
Autonomous mobile robot (AMR) deployments are no exception. Each new data access point to your enterprise network—individual robots, fleet management software, and third-party integrations—introduces potential vulnerabilities that require security measures. A holistic, end-to-end security strategy looks at how to safeguard these access points through authentication, data protection, and encrypted communications to ensure there are no weak entry points that could put your entire network at risk.
In this blog, we’ll explore key security considerations for AMRs, fleet management software, and third-party integrations, focusing on how authentication, data protection, and encrypted communications can help keep your network safe.
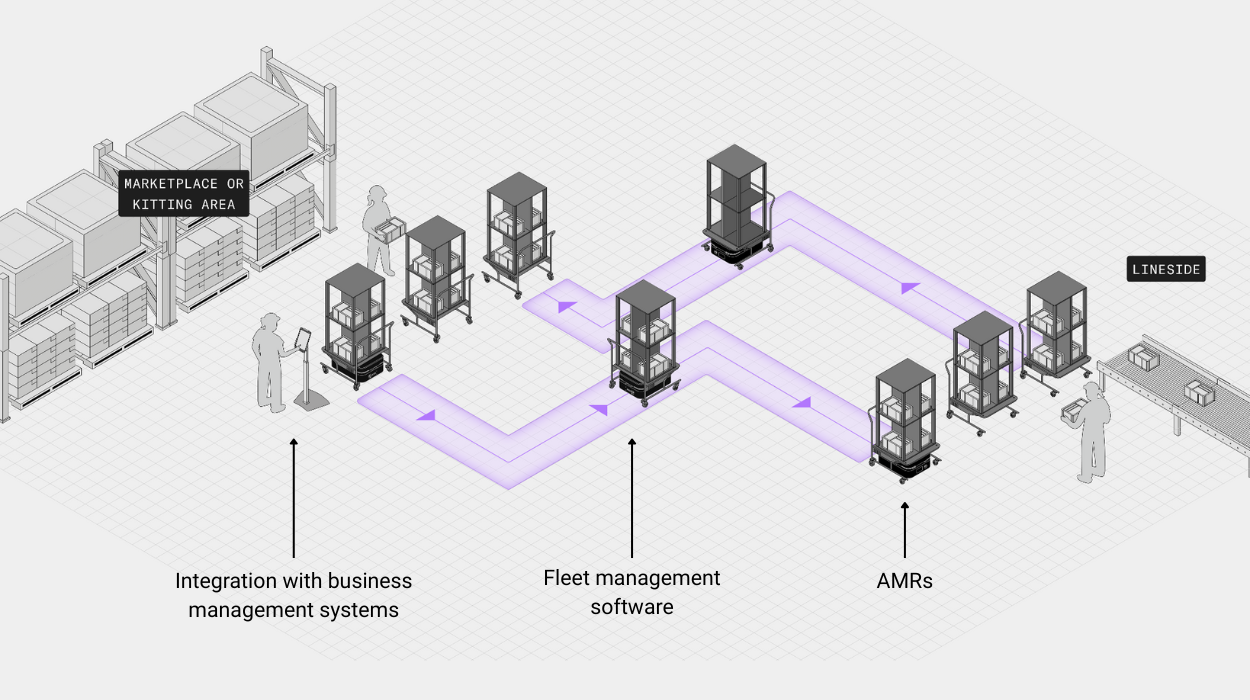
Image 1: Security considerations need to be evaluated at each data access point: AMRs, fleet management software, and integration with business management systems.
1. Security elements for autonomous mobile robots (AMRs)
AMRs operate at both local and network levels, processing and storing sensitive data such as maps, sensor readings, and job logs. Access to the local AMR software and data—whether through a software interface or through the hardware ports—should be authenticated, authorized, and encrypted.
Securing these access points is essential:
- Authentication: Access to AMR software interfaces over Wi-Fi should be authenticated and authorized through software-based controls, while Ethernet access should be restricted through firewall and network-based protections to prevent unauthorized entry.
- Data protection: Communication between AMRs and the fleet management software should be encrypted to protect local AMR data and fleet data during transmission. Your vendor should have checks in place to ensure the robot starts in a trusted state.
- Encrypted communication: Wireless communication is a common attack vector. All Wi-Fi traffic between AMRs and other systems should use HTTPS with SSL/TLS encryption to prevent interception or spoofing.
2. Security elements for fleet management software
The fleet management software is the central hub that connects the entire solution, orchestrating data access and communication encryption across the system. It holds user credentials, maps, job queues, and logs while communicating data with AMRs and third-party systems. Its security posture directly impacts the entire deployment:
- Authentication: Implement Single Sign-On (SSO) solutions such as LDAP or Okta for user verification, supplemented by audit logs to track and prevent unauthorized access.
- Data protection: Secure cloud or data center environments with firewalls, intrusion detection systems, and network segmentation.
- Encrypted communication: All data exchanges between fleet management software, AMRs, and external systems should enforce SSL/TLS encryption. This ensures sensitive operational data remains confidential during transmission.
3. Security elements for third-party integrations (ERP, MES, WMS)
APIs serve as gateways for exchanging task and location data, making them critical points for security enforcement in AMR integrations that enable seamless operations:
- Authentication: Validate API requests using OPC-UA authentication, API keys, and web tokens. Restrict access to authorized systems only and implement client token requests to control which systems can send or receive data.
- Data protection: Encrypt all data in transit. Apply strict access controls to ensure only approved systems can interact with AMR-related data.
- Encrypted communication: Use HTTPS/TLS for all API calls to safeguard data during transmission. This prevents interception and ensures secure interoperability across platforms.
End-to-end collaboration
Data security is an interconnected, end-to-end approach focused on managing exposure to risk. Your AMR vendor should act as an extension of your IT team, collaborating to assess risks, build a multi-layered security framework, and maintain continuous threat monitoring and response.
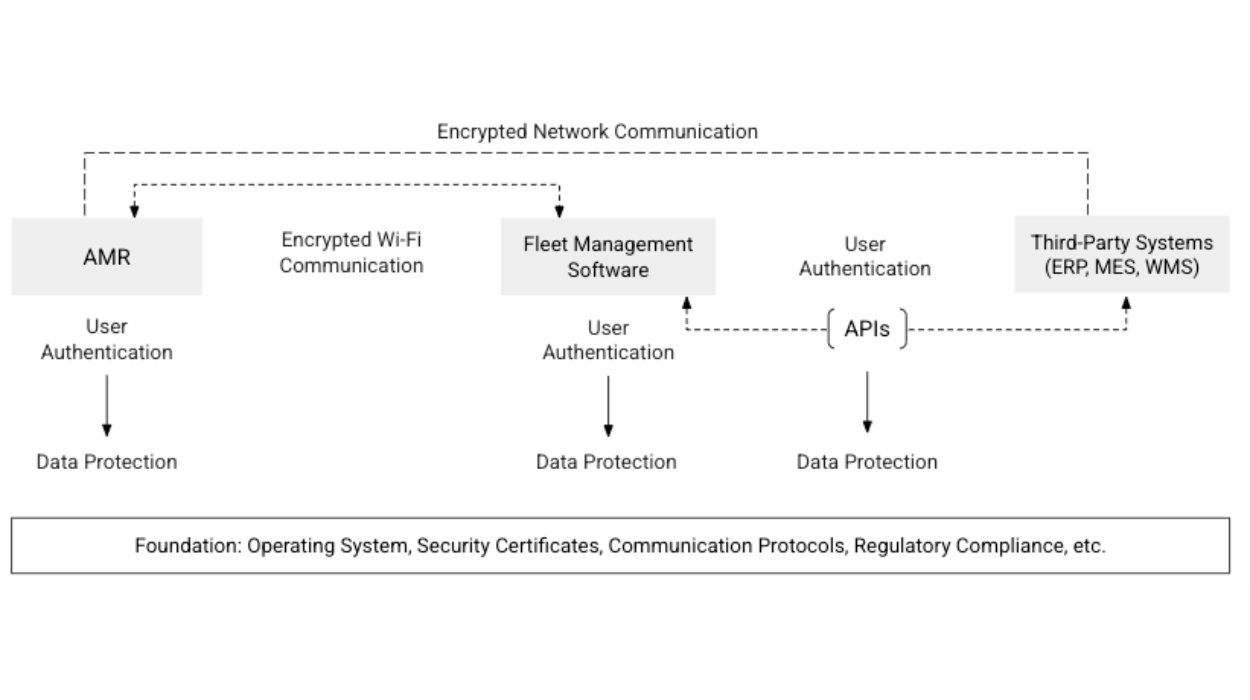
Image 2: Security is an end-to-end process that requires close collaboration with your AMR vendor.
By prioritizing authentication, data protection, and encrypted communication across AMRs, fleet management software, and third-party integrations, manufacturers can reduce risk exposure and ensure operational continuity in an increasingly connected industrial landscape.
To learn more about AMR security considerations, watch the full webinar “From pilot to enterprise fleet: How to scale AMRs successfully.”
Subscribe to our newsletter
Stay in the loop on product news, case studies, upcoming events and more.







